 The rise of the Internet has engendered the formation of illicit markets online, where individuals can sell a variety of products and services offered via forums and websites. Some of the first research in this area considered the ways that hackers directly sold data they acquired through hacks, data breaches, and phishing direct to others through advertisements in IRC channels or web forums (Holt and Lampke, 2010; Franklin, Paxson, Perrig, and Savage, 2007; Motoyama, McCoy, Levchenko, Savage, and Voelker, 2011; Thomas and Martin, 2006). These markets appear to be hosted and operated primarily out of Russia and Eastern Europe, though a small proportion exist in the US and parts of Western Europe (Dunn, 2012; Symantec Corporation, 2012). Individuals commonly sell credit card and debit card accounts, PIN numbers, and supporting customer information from around the world in bulk lots (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011). Some also offer “cash out” services to obtain physical money from electronic accounts by hijacking these accounts to engage in electronic fund transfers established by a hacker (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011; Thomas and Martin, 2006). Others offer “drops services,” whereby individuals purchase electronics and other goods electronically using stolen cards, have them shipped to intermediaries who pawn the items, and then wire the cash to interested parties (Holt and Lampke, 2010). A limited number of sellers also offer spam lists and malicious software tools that can be used to engage in fraud (Holt and Lampke, 2010).
These markets also provide individuals with access to cybercrime tools, such as malicious software and hacking resources, on a fee-for-service basis. For instance, individuals could purchase access to botnet malware, Trojan horse programs, and a variety of exploit kits that enable actors to engage in sophisticated attacks (e.g. Dupont et al., 2017; Holt, 2013). Should a person not have the skills needed to operate their own long-term hacking schemes, individuals also lease out access to tools that will enable attacks on their behalf, such as the use of Distributed Denial of Service attacks that knock websites off-line for extended periods of time (Holt, 2013: Hutchings & Clayton, 2016).
These markets pose a unique threat to the safety and security of cyberspace as they provide venues for vendors to monetize their skills while concurrently providing individuals with a means to engage in sophisticated forms of cybercrime and identity theft with minimal effort and limited technical knowledge or skill (Franklin et al., 2007; Holt and Lampke, 2010; Motoyama et al., 2011). In addition, markets create opportunities for victims to be affected multiple times whether through repeat attacks or by removing individuals’ ability to control access to their Personally Identifiable Information.
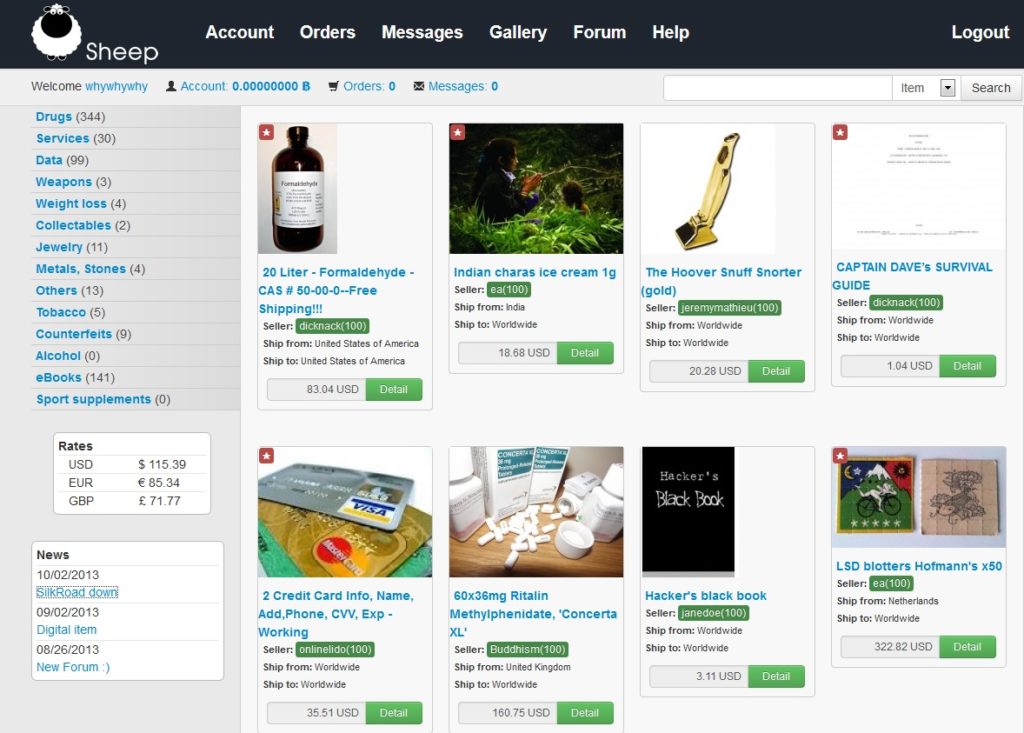
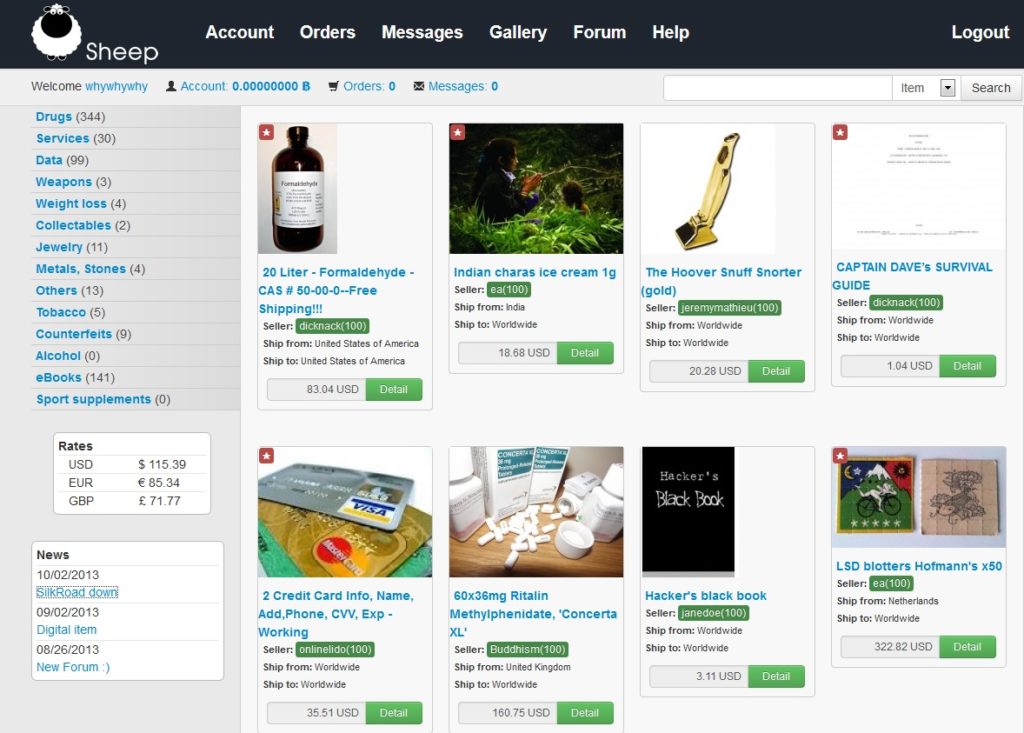
Over the last 10 years, there has also been growth in the trafficking of illicit narcotics like cocaine, marijuana, and methamphetamines through online markets operating on the so-called Dark Web, which is a portion of the Internet that can only be accessed via the use of specialized encryption software and browser protocols. Unlike the open web, individuals can only access these forums through the use of The Onion Router, or TOR service, which is a free proxy and encryption protocol that hides the IP address and location details of the user (Barratt, Ferris, & Winstock 2014; Dolliver 2015). These markets are further insulated by the fact that they cannot be indexed by google or other search engines. As a result, this technology limits the ability of law enforcement agencies to eliminate illicit content because the hosting source cannot be identified through traditional means (Dolliver 2015; Estes, 2014).
One of the first Tor-based narcotics markets that gained prominence was called the Silk Road. The market gained attention from researchers and the popular media due to the nature of the products sold, and the fact that transactions were paid using bitcoins, a relatively anonymous form of electronic currency (Franklin, 2013). As the Silk Road gained prominence as a venue for the sale of various narcotics, law enforcement agencies in both the US and Australia conducted sting operations against buyers. In fact, since it opened in 2011 the Silk Road enabled over one million transactions worth an estimated $1.2 billion in revenue (Barratt, 2012).
The subsequent take down of the Silk Road has led to a diffuse number of replacement markets on the Dark Web to sell narcotics, as well as other physical goods such as identity documents and firearms (e.g. Hetu & Dore, 2017; Moeller, Munksgaard, & Demant, 2017; von Buskirk, Roxbury, Farrell, & Burns, 2014). There is also limited evidence to suggest hackers sell products on the Dark Web, though not to the same degree as on the open web (e.g. Smirnova & Holt, 2017). Both open and dark markets also share some common operational characteristics, such as the use of on-line payment systems and customer feedback mechanisms such as product reviews in order to establish vendor credibility.
There is, however, little research that directly compares the operations of physical and digital goods vendors on the Open and Dark Web using empirical data (for an exception see Smirnova & Holt, 2017). While studies have developed small and large samples of posts made in on-line markets for qualitative (e.g. Barratt, 2012; Holt 2013; Holt et al., 2016) and quantitative analyses (e.g. Dupont et al., 2017; Barratt, Ferris, & WInstock, 2016; Franklin, 2007; Holt & Smirnova, 2016; Motoyama et al., 2011), these studies make no attempt to compare the economic operations of these product markets, particularly the scope of transactions completed by buyers and sellers. Additionally, while research has considered the social organization and network composition of both stolen data markets (e.g. Holt, Smirnova, & Chua, 2016; Motoyama et al., 2011; Yip et al., 2013) and drug markets (Bright, Hughes, & Chalmers, 2012), few have compared the network structures of actors across these market types. Few have also considered differences in the operational composition of actors across Open and Dark Web markets and their potential implications for formal and informal law enforcement disruption methods generally (see Hutchings & Holt, 2017).
Thus this study will attempt to address this key gap in the research literature through an analysis of a large comparative analysis of posts made in both digital and physical goods markets operating on both the Open and Dark Web. The research team will use qualitative and quantitative methods to examine the economic variations within and across markets, as well as their organizational structures using both social network analyses and qualitative social organization frameworks. This will provide historical data and trends in market products, payment systems, and vendor and seller interactions.
The rise of the Internet has engendered the formation of illicit markets online, where individuals can sell a variety of products and services offered via forums and websites. Some of the first research in this area considered the ways that hackers directly sold data they acquired through hacks, data breaches, and phishing direct to others through advertisements in IRC channels or web forums (Holt and Lampke, 2010; Franklin, Paxson, Perrig, and Savage, 2007; Motoyama, McCoy, Levchenko, Savage, and Voelker, 2011; Thomas and Martin, 2006). These markets appear to be hosted and operated primarily out of Russia and Eastern Europe, though a small proportion exist in the US and parts of Western Europe (Dunn, 2012; Symantec Corporation, 2012). Individuals commonly sell credit card and debit card accounts, PIN numbers, and supporting customer information from around the world in bulk lots (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011). Some also offer “cash out” services to obtain physical money from electronic accounts by hijacking these accounts to engage in electronic fund transfers established by a hacker (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011; Thomas and Martin, 2006). Others offer “drops services,” whereby individuals purchase electronics and other goods electronically using stolen cards, have them shipped to intermediaries who pawn the items, and then wire the cash to interested parties (Holt and Lampke, 2010). A limited number of sellers also offer spam lists and malicious software tools that can be used to engage in fraud (Holt and Lampke, 2010).
These markets also provide individuals with access to cybercrime tools, such as malicious software and hacking resources, on a fee-for-service basis. For instance, individuals could purchase access to botnet malware, Trojan horse programs, and a variety of exploit kits that enable actors to engage in sophisticated attacks (e.g. Dupont et al., 2017; Holt, 2013). Should a person not have the skills needed to operate their own long-term hacking schemes, individuals also lease out access to tools that will enable attacks on their behalf, such as the use of Distributed Denial of Service attacks that knock websites off-line for extended periods of time (Holt, 2013: Hutchings & Clayton, 2016).
These markets pose a unique threat to the safety and security of cyberspace as they provide venues for vendors to monetize their skills while concurrently providing individuals with a means to engage in sophisticated forms of cybercrime and identity theft with minimal effort and limited technical knowledge or skill (Franklin et al., 2007; Holt and Lampke, 2010; Motoyama et al., 2011). In addition, markets create opportunities for victims to be affected multiple times whether through repeat attacks or by removing individuals’ ability to control access to their Personally Identifiable Information.
Over the last 10 years, there has also been growth in the trafficking of illicit narcotics like cocaine, marijuana, and methamphetamines through online markets operating on the so-called Dark Web, which is a portion of the Internet that can only be accessed via the use of specialized encryption software and browser protocols. Unlike the open web, individuals can only access these forums through the use of The Onion Router, or TOR service, which is a free proxy and encryption protocol that hides the IP address and location details of the user (Barratt, Ferris, & Winstock 2014; Dolliver 2015). These markets are further insulated by the fact that they cannot be indexed by google or other search engines. As a result, this technology limits the ability of law enforcement agencies to eliminate illicit content because the hosting source cannot be identified through traditional means (Dolliver 2015; Estes, 2014).
One of the first Tor-based narcotics markets that gained prominence was called the Silk Road. The market gained attention from researchers and the popular media due to the nature of the products sold, and the fact that transactions were paid using bitcoins, a relatively anonymous form of electronic currency (Franklin, 2013). As the Silk Road gained prominence as a venue for the sale of various narcotics, law enforcement agencies in both the US and Australia conducted sting operations against buyers. In fact, since it opened in 2011 the Silk Road enabled over one million transactions worth an estimated $1.2 billion in revenue (Barratt, 2012).
The subsequent take down of the Silk Road has led to a diffuse number of replacement markets on the Dark Web to sell narcotics, as well as other physical goods such as identity documents and firearms (e.g. Hetu & Dore, 2017; Moeller, Munksgaard, & Demant, 2017; von Buskirk, Roxbury, Farrell, & Burns, 2014). There is also limited evidence to suggest hackers sell products on the Dark Web, though not to the same degree as on the open web (e.g. Smirnova & Holt, 2017). Both open and dark markets also share some common operational characteristics, such as the use of on-line payment systems and customer feedback mechanisms such as product reviews in order to establish vendor credibility.
There is, however, little research that directly compares the operations of physical and digital goods vendors on the Open and Dark Web using empirical data (for an exception see Smirnova & Holt, 2017). While studies have developed small and large samples of posts made in on-line markets for qualitative (e.g. Barratt, 2012; Holt 2013; Holt et al., 2016) and quantitative analyses (e.g. Dupont et al., 2017; Barratt, Ferris, & WInstock, 2016; Franklin, 2007; Holt & Smirnova, 2016; Motoyama et al., 2011), these studies make no attempt to compare the economic operations of these product markets, particularly the scope of transactions completed by buyers and sellers. Additionally, while research has considered the social organization and network composition of both stolen data markets (e.g. Holt, Smirnova, & Chua, 2016; Motoyama et al., 2011; Yip et al., 2013) and drug markets (Bright, Hughes, & Chalmers, 2012), few have compared the network structures of actors across these market types. Few have also considered differences in the operational composition of actors across Open and Dark Web markets and their potential implications for formal and informal law enforcement disruption methods generally (see Hutchings & Holt, 2017).
Thus this study will attempt to address this key gap in the research literature through an analysis of a large comparative analysis of posts made in both digital and physical goods markets operating on both the Open and Dark Web. The research team will use qualitative and quantitative methods to examine the economic variations within and across markets, as well as their organizational structures using both social network analyses and qualitative social organization frameworks. This will provide historical data and trends in market products, payment systems, and vendor and seller interactions. Understanding the Economy and Social Organization of the Underground Market for Cybercrime as a Service
- Project Fact Sheet
 The rise of the Internet has engendered the formation of illicit markets online, where individuals can sell a variety of products and services offered via forums and websites. Some of the first research in this area considered the ways that hackers directly sold data they acquired through hacks, data breaches, and phishing direct to others through advertisements in IRC channels or web forums (Holt and Lampke, 2010; Franklin, Paxson, Perrig, and Savage, 2007; Motoyama, McCoy, Levchenko, Savage, and Voelker, 2011; Thomas and Martin, 2006). These markets appear to be hosted and operated primarily out of Russia and Eastern Europe, though a small proportion exist in the US and parts of Western Europe (Dunn, 2012; Symantec Corporation, 2012). Individuals commonly sell credit card and debit card accounts, PIN numbers, and supporting customer information from around the world in bulk lots (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011). Some also offer “cash out” services to obtain physical money from electronic accounts by hijacking these accounts to engage in electronic fund transfers established by a hacker (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011; Thomas and Martin, 2006). Others offer “drops services,” whereby individuals purchase electronics and other goods electronically using stolen cards, have them shipped to intermediaries who pawn the items, and then wire the cash to interested parties (Holt and Lampke, 2010). A limited number of sellers also offer spam lists and malicious software tools that can be used to engage in fraud (Holt and Lampke, 2010).
These markets also provide individuals with access to cybercrime tools, such as malicious software and hacking resources, on a fee-for-service basis. For instance, individuals could purchase access to botnet malware, Trojan horse programs, and a variety of exploit kits that enable actors to engage in sophisticated attacks (e.g. Dupont et al., 2017; Holt, 2013). Should a person not have the skills needed to operate their own long-term hacking schemes, individuals also lease out access to tools that will enable attacks on their behalf, such as the use of Distributed Denial of Service attacks that knock websites off-line for extended periods of time (Holt, 2013: Hutchings & Clayton, 2016).
These markets pose a unique threat to the safety and security of cyberspace as they provide venues for vendors to monetize their skills while concurrently providing individuals with a means to engage in sophisticated forms of cybercrime and identity theft with minimal effort and limited technical knowledge or skill (Franklin et al., 2007; Holt and Lampke, 2010; Motoyama et al., 2011). In addition, markets create opportunities for victims to be affected multiple times whether through repeat attacks or by removing individuals’ ability to control access to their Personally Identifiable Information.
Over the last 10 years, there has also been growth in the trafficking of illicit narcotics like cocaine, marijuana, and methamphetamines through online markets operating on the so-called Dark Web, which is a portion of the Internet that can only be accessed via the use of specialized encryption software and browser protocols. Unlike the open web, individuals can only access these forums through the use of The Onion Router, or TOR service, which is a free proxy and encryption protocol that hides the IP address and location details of the user (Barratt, Ferris, & Winstock 2014; Dolliver 2015). These markets are further insulated by the fact that they cannot be indexed by google or other search engines. As a result, this technology limits the ability of law enforcement agencies to eliminate illicit content because the hosting source cannot be identified through traditional means (Dolliver 2015; Estes, 2014).
One of the first Tor-based narcotics markets that gained prominence was called the Silk Road. The market gained attention from researchers and the popular media due to the nature of the products sold, and the fact that transactions were paid using bitcoins, a relatively anonymous form of electronic currency (Franklin, 2013). As the Silk Road gained prominence as a venue for the sale of various narcotics, law enforcement agencies in both the US and Australia conducted sting operations against buyers. In fact, since it opened in 2011 the Silk Road enabled over one million transactions worth an estimated $1.2 billion in revenue (Barratt, 2012).
The subsequent take down of the Silk Road has led to a diffuse number of replacement markets on the Dark Web to sell narcotics, as well as other physical goods such as identity documents and firearms (e.g. Hetu & Dore, 2017; Moeller, Munksgaard, & Demant, 2017; von Buskirk, Roxbury, Farrell, & Burns, 2014). There is also limited evidence to suggest hackers sell products on the Dark Web, though not to the same degree as on the open web (e.g. Smirnova & Holt, 2017). Both open and dark markets also share some common operational characteristics, such as the use of on-line payment systems and customer feedback mechanisms such as product reviews in order to establish vendor credibility.
There is, however, little research that directly compares the operations of physical and digital goods vendors on the Open and Dark Web using empirical data (for an exception see Smirnova & Holt, 2017). While studies have developed small and large samples of posts made in on-line markets for qualitative (e.g. Barratt, 2012; Holt 2013; Holt et al., 2016) and quantitative analyses (e.g. Dupont et al., 2017; Barratt, Ferris, & WInstock, 2016; Franklin, 2007; Holt & Smirnova, 2016; Motoyama et al., 2011), these studies make no attempt to compare the economic operations of these product markets, particularly the scope of transactions completed by buyers and sellers. Additionally, while research has considered the social organization and network composition of both stolen data markets (e.g. Holt, Smirnova, & Chua, 2016; Motoyama et al., 2011; Yip et al., 2013) and drug markets (Bright, Hughes, & Chalmers, 2012), few have compared the network structures of actors across these market types. Few have also considered differences in the operational composition of actors across Open and Dark Web markets and their potential implications for formal and informal law enforcement disruption methods generally (see Hutchings & Holt, 2017).
Thus this study will attempt to address this key gap in the research literature through an analysis of a large comparative analysis of posts made in both digital and physical goods markets operating on both the Open and Dark Web. The research team will use qualitative and quantitative methods to examine the economic variations within and across markets, as well as their organizational structures using both social network analyses and qualitative social organization frameworks. This will provide historical data and trends in market products, payment systems, and vendor and seller interactions.
The rise of the Internet has engendered the formation of illicit markets online, where individuals can sell a variety of products and services offered via forums and websites. Some of the first research in this area considered the ways that hackers directly sold data they acquired through hacks, data breaches, and phishing direct to others through advertisements in IRC channels or web forums (Holt and Lampke, 2010; Franklin, Paxson, Perrig, and Savage, 2007; Motoyama, McCoy, Levchenko, Savage, and Voelker, 2011; Thomas and Martin, 2006). These markets appear to be hosted and operated primarily out of Russia and Eastern Europe, though a small proportion exist in the US and parts of Western Europe (Dunn, 2012; Symantec Corporation, 2012). Individuals commonly sell credit card and debit card accounts, PIN numbers, and supporting customer information from around the world in bulk lots (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011). Some also offer “cash out” services to obtain physical money from electronic accounts by hijacking these accounts to engage in electronic fund transfers established by a hacker (Holt and Lampke, 2010; Franklin et al., 2007; Motoyama et al., 2011; Thomas and Martin, 2006). Others offer “drops services,” whereby individuals purchase electronics and other goods electronically using stolen cards, have them shipped to intermediaries who pawn the items, and then wire the cash to interested parties (Holt and Lampke, 2010). A limited number of sellers also offer spam lists and malicious software tools that can be used to engage in fraud (Holt and Lampke, 2010).
These markets also provide individuals with access to cybercrime tools, such as malicious software and hacking resources, on a fee-for-service basis. For instance, individuals could purchase access to botnet malware, Trojan horse programs, and a variety of exploit kits that enable actors to engage in sophisticated attacks (e.g. Dupont et al., 2017; Holt, 2013). Should a person not have the skills needed to operate their own long-term hacking schemes, individuals also lease out access to tools that will enable attacks on their behalf, such as the use of Distributed Denial of Service attacks that knock websites off-line for extended periods of time (Holt, 2013: Hutchings & Clayton, 2016).
These markets pose a unique threat to the safety and security of cyberspace as they provide venues for vendors to monetize their skills while concurrently providing individuals with a means to engage in sophisticated forms of cybercrime and identity theft with minimal effort and limited technical knowledge or skill (Franklin et al., 2007; Holt and Lampke, 2010; Motoyama et al., 2011). In addition, markets create opportunities for victims to be affected multiple times whether through repeat attacks or by removing individuals’ ability to control access to their Personally Identifiable Information.
Over the last 10 years, there has also been growth in the trafficking of illicit narcotics like cocaine, marijuana, and methamphetamines through online markets operating on the so-called Dark Web, which is a portion of the Internet that can only be accessed via the use of specialized encryption software and browser protocols. Unlike the open web, individuals can only access these forums through the use of The Onion Router, or TOR service, which is a free proxy and encryption protocol that hides the IP address and location details of the user (Barratt, Ferris, & Winstock 2014; Dolliver 2015). These markets are further insulated by the fact that they cannot be indexed by google or other search engines. As a result, this technology limits the ability of law enforcement agencies to eliminate illicit content because the hosting source cannot be identified through traditional means (Dolliver 2015; Estes, 2014).
One of the first Tor-based narcotics markets that gained prominence was called the Silk Road. The market gained attention from researchers and the popular media due to the nature of the products sold, and the fact that transactions were paid using bitcoins, a relatively anonymous form of electronic currency (Franklin, 2013). As the Silk Road gained prominence as a venue for the sale of various narcotics, law enforcement agencies in both the US and Australia conducted sting operations against buyers. In fact, since it opened in 2011 the Silk Road enabled over one million transactions worth an estimated $1.2 billion in revenue (Barratt, 2012).
The subsequent take down of the Silk Road has led to a diffuse number of replacement markets on the Dark Web to sell narcotics, as well as other physical goods such as identity documents and firearms (e.g. Hetu & Dore, 2017; Moeller, Munksgaard, & Demant, 2017; von Buskirk, Roxbury, Farrell, & Burns, 2014). There is also limited evidence to suggest hackers sell products on the Dark Web, though not to the same degree as on the open web (e.g. Smirnova & Holt, 2017). Both open and dark markets also share some common operational characteristics, such as the use of on-line payment systems and customer feedback mechanisms such as product reviews in order to establish vendor credibility.
There is, however, little research that directly compares the operations of physical and digital goods vendors on the Open and Dark Web using empirical data (for an exception see Smirnova & Holt, 2017). While studies have developed small and large samples of posts made in on-line markets for qualitative (e.g. Barratt, 2012; Holt 2013; Holt et al., 2016) and quantitative analyses (e.g. Dupont et al., 2017; Barratt, Ferris, & WInstock, 2016; Franklin, 2007; Holt & Smirnova, 2016; Motoyama et al., 2011), these studies make no attempt to compare the economic operations of these product markets, particularly the scope of transactions completed by buyers and sellers. Additionally, while research has considered the social organization and network composition of both stolen data markets (e.g. Holt, Smirnova, & Chua, 2016; Motoyama et al., 2011; Yip et al., 2013) and drug markets (Bright, Hughes, & Chalmers, 2012), few have compared the network structures of actors across these market types. Few have also considered differences in the operational composition of actors across Open and Dark Web markets and their potential implications for formal and informal law enforcement disruption methods generally (see Hutchings & Holt, 2017).
Thus this study will attempt to address this key gap in the research literature through an analysis of a large comparative analysis of posts made in both digital and physical goods markets operating on both the Open and Dark Web. The research team will use qualitative and quantitative methods to examine the economic variations within and across markets, as well as their organizational structures using both social network analyses and qualitative social organization frameworks. This will provide historical data and trends in market products, payment systems, and vendor and seller interactions. 